Security Audit (Studio)
Suite
Customer Experience
Product
Qualtrics
What's on this page
About the Security Audit Page
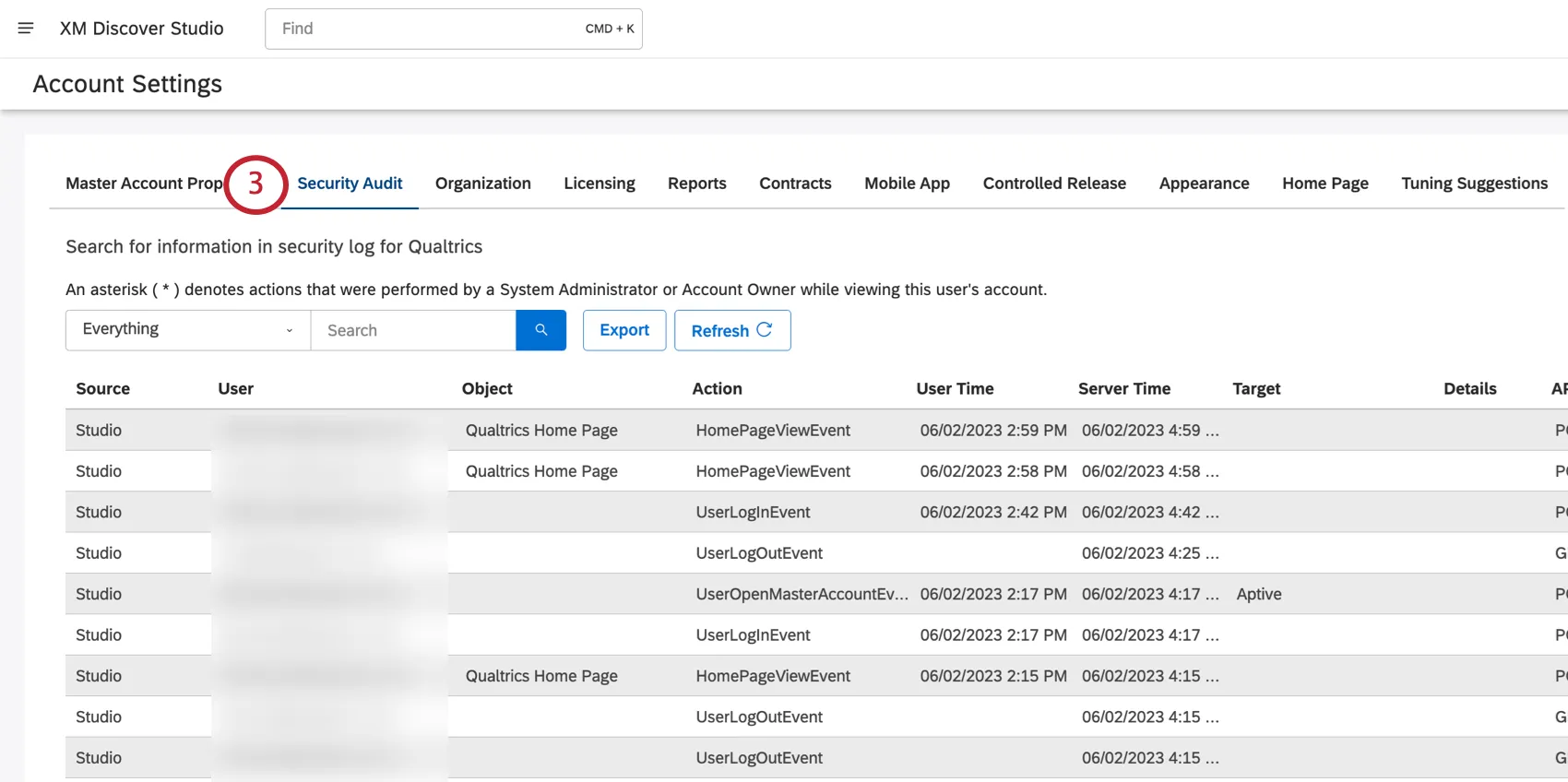
The Security Audit page keeps track of many different events that have happened in your master account for the last 6 months.
You can view the security log, search for specific events, and export them to Excel. This information can help you monitor adoption and usage of Studio, as well as troubleshoot issues with the XM Discover support team.
Qtip: You can use administrative reporting to track account usage and activity.
Qtip: You need a Conduct Security Audit permission to access the security log.
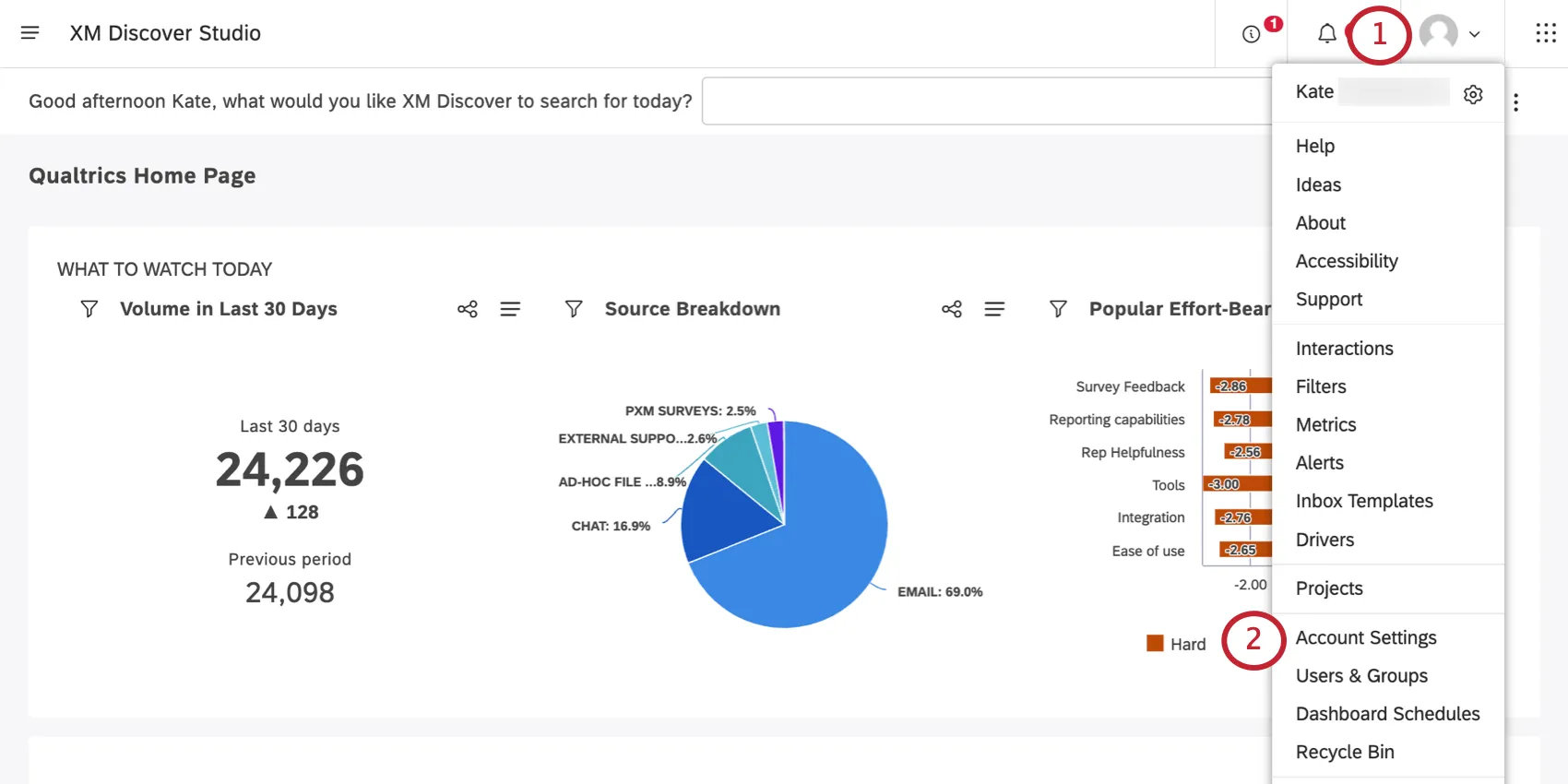
Accessing the Security Log
To update the security log on demand, click the Refresh button.
Qtip: You can sort events by clicking any column’s heading. By default, the log is sorted in reverse chronological order, with the most recent events at the top.
Information in Security Audit Records
You’ll see the following column of information for each entry in the security log:
- Source: The name of the XM Discover application where the action happened. Currently, Studio is the only option.
- User: The user who performed the action logged here.
- Object: The object of the action (where applicable). Example: When a user views a dashboard, the name of the dashboard is listed in the Object column.
- Action: Name of the action. For a detailed list, see Actions Included in the Security Log (Studio). Qtip: An asterisk ( * ) in front of the action name means it was performed by a system administrator proxy logging in as a certain user.
- User Time: The timestamp of the event according to the user’s time zone.
- Server Time: The timestamp of the event according to the server’s time zone.
- Target: The details related to the action (where applicable). Example: When a user modifies a master account property, the name of the master account is listed in the Object column, and the name of the property is listed in the Target column.
- Details: Additional details, such as a reason for the document deletion, or the method of dashboard creation.
- API Call: API method used.
- HTTP Response: The status code returned by the server.
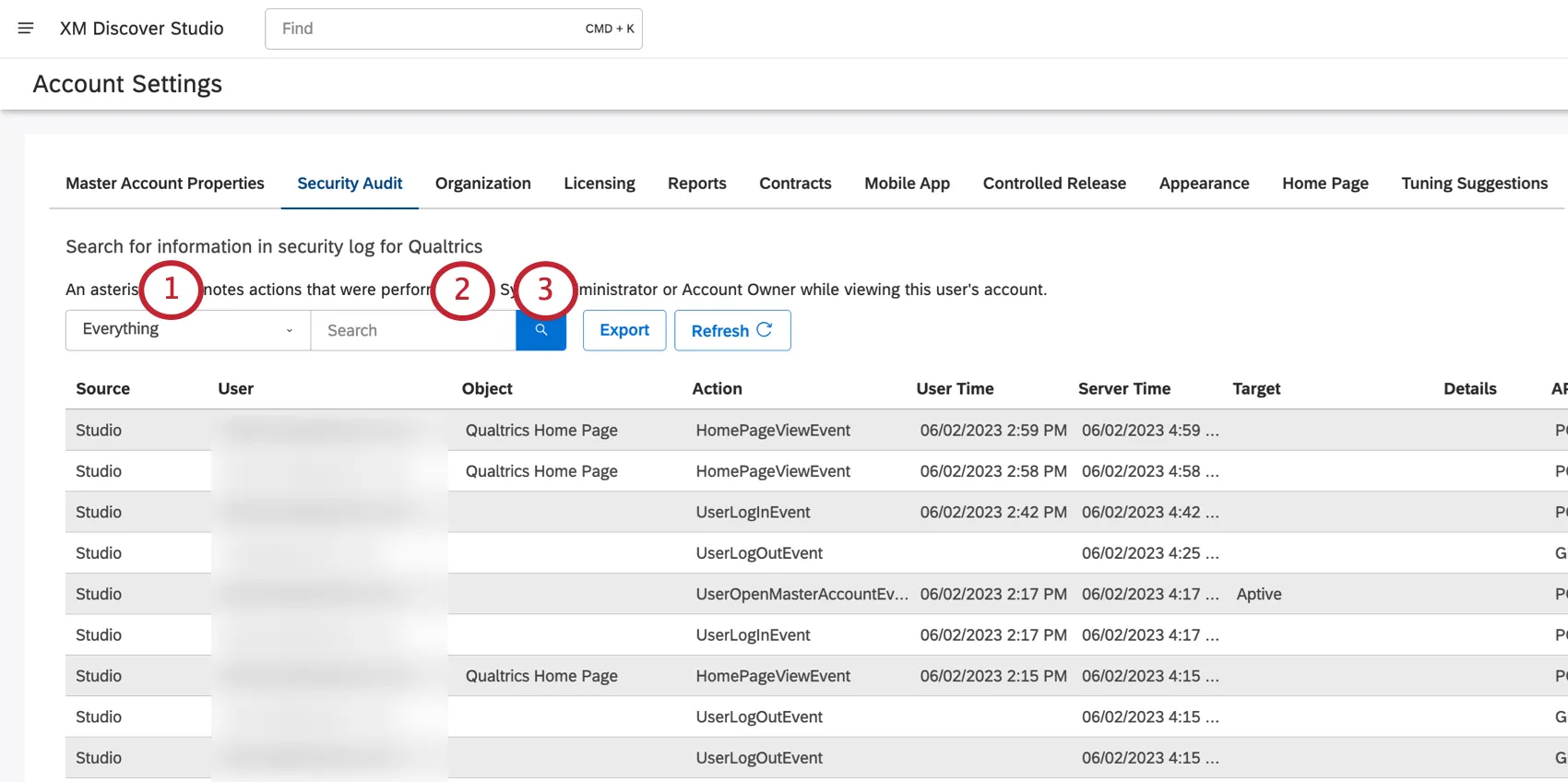
Searching the Security Log
You can search the security log for events that happened within the last 6 months.
Qtip: Any search applied will be used in the security audit export.
Example: The following search query returns all actions performed by John Smith within the last 6 months:
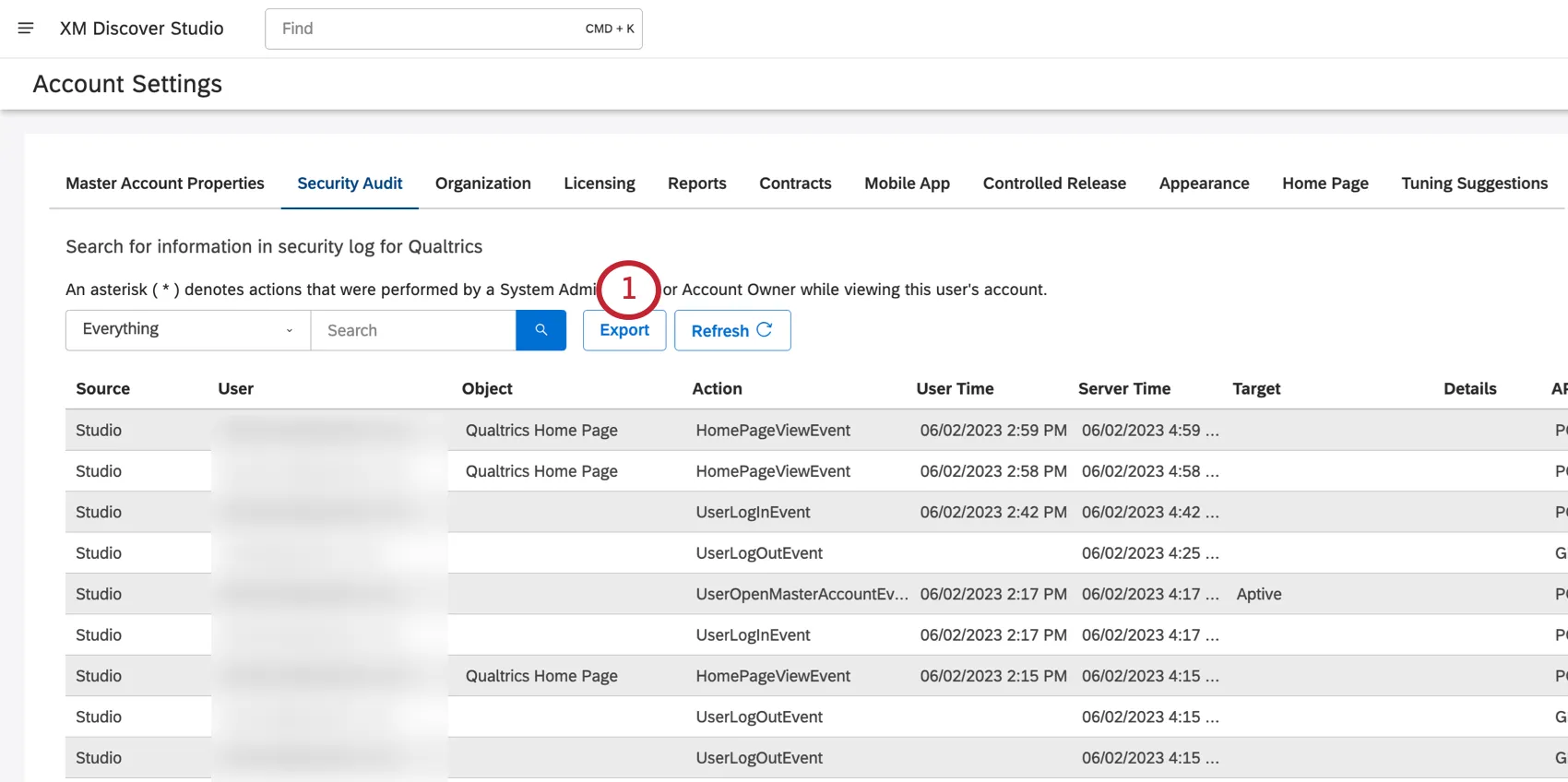
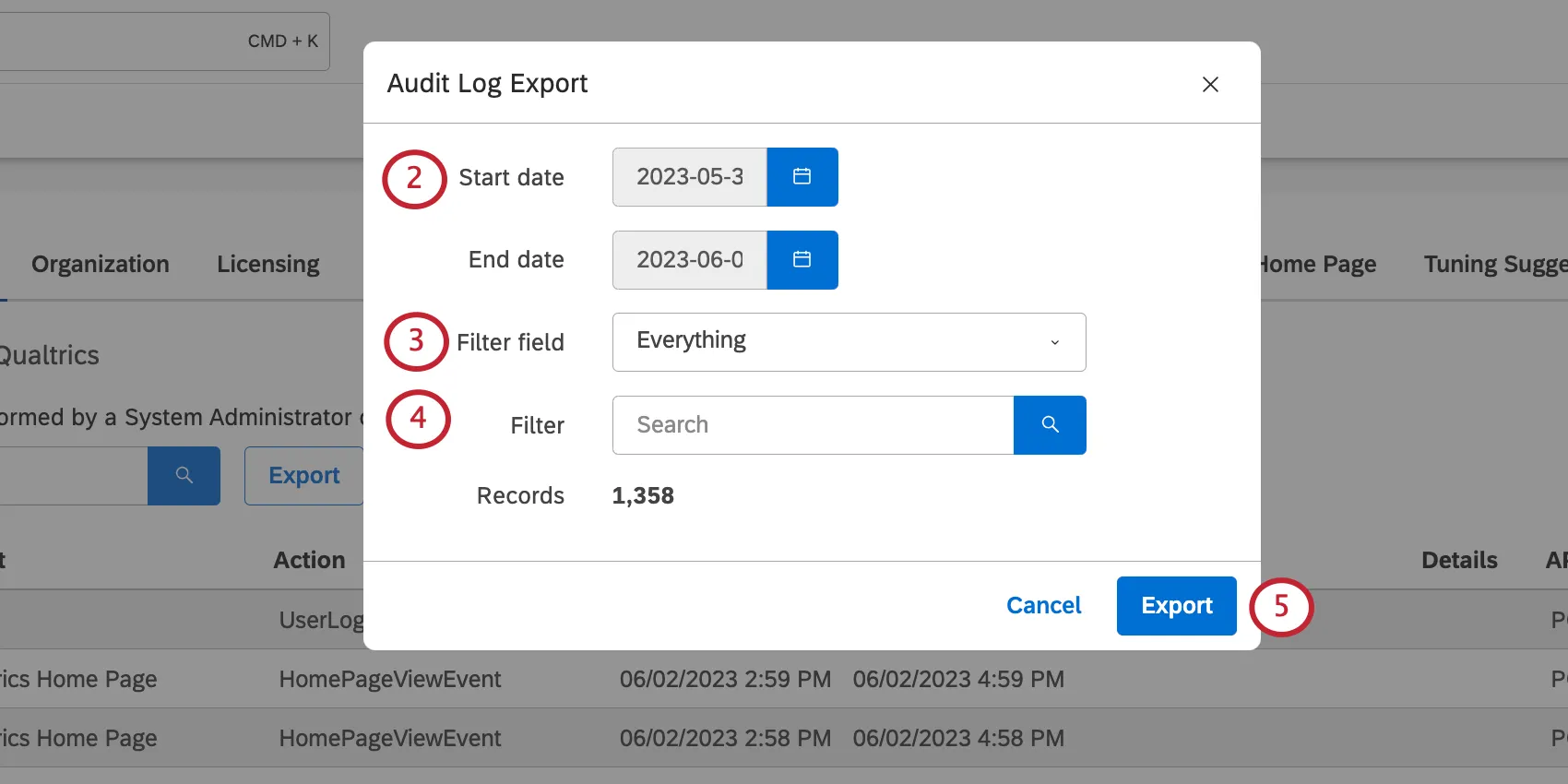
Exporting the Security Log
You can export the security log to an XLSX spreadsheet (Excel).
Qtip: If you apply any search criteria to the security log, it is automatically carried over to the export.
That's great! Thank you for your feedback!
Thank you for your feedback!